Apache Tomcat is deployed as the Web Application server of choice for Dashboards.
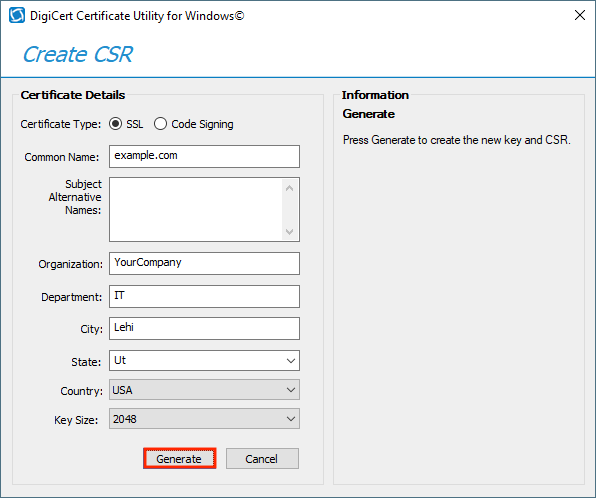
The keystore type is JKS, I've verified it through the command., Press Shift + right-click to open command pront: write this keytool.exe -genkey -alias tomcat. In order to generate the CSR code on Tomcat, you can use keytool commands. First, you need to create a keystore that will contain the private key. Open up a command line interface and run the following command: keytool -genkey -keysize 2048 -keyalg RSA -alias tomcat -keystore yourkeystore.jks.
By default the Tomcat instance is configured to serve content over HTTP but it can be configured on deploy to use HTTPS (SSL) instead.
The steps required to enable HTTPS/SSL are described in this section.
Java Keystore
Tomcat Connector Keystore Type
In order to enable SSL on the Tomcat deploy you must provide a Java Keystore which contains the required certificates, You can generate a keystore using the following instructions from the Tomcat docs here.
Tomcat SSL Configuration - Linux
Tomcat 7 Keystore Type Pkcs12
Tomcat Configuration
To install and configure SSL/TLS support on Tomcat, you need to follow these steps.
Specify a secure password.
Bundle Deploy
If you are deploying your environment using the Bundle installer you can enable HTTPS at deploy time by selecting option 2 here:
You will then be prompted for the location of your java keystore and the password using whilst generating the keystore.
Then the HTTP and HTTPS ports for the Web Server.
Note: The HTTP connector will forward connections to the HTTPS connector when enabled.
Custom Deploy
If you are a custom install config change the app-server-install-type to 2, add the tomcat-keystore-file and tomcat-keystore-password and update the path to the keystore and the keystore password.
Tomcat HTTPS with APR Connector
Apache tomcat 5.5. Tomcat can be configured to use the Apache Portable Runtime (APR) based Native library which uses SSL Certificates instead of the standard Java Keystore.
Note: This option is only available when using a custom install config
The APR library and associated dependencies must be deployed on your host before using this option. See Tomcat documentation here.
With the library in place you will require the following certificates and key files:
| Name | Description |
|---|---|
| server-crt.pem | Server Certificate file |
| server-key.pem | Server Key file |
| ca.pem | Certificate Authority file |
The files above should be referenced in your install.config file as follows:
Note: In order to enable the installation of this connector the following must also be set:
Once the install has completed the connector in the Tomcat server.xml should look something like this:
Tomcat HTTPS with kdb+ TLS
If you are deploying with TLS enabled for kdb+ and HTTPS enabled for Tomcat there are additional considerations. For both of these to work the install script needs to export the cert used for the HTTPS connector out of the keystore defined below:
If you have created the keystore using the instructions above the certificate extracted will have the alias 'tomcat'. Drupal 8 docker download. The install log will contain:
If you are using a keystore which contains a different alias for the key, the install will fail and you will see the following:
With the alias changed you should see:
The connector cert is then imported into the keystore used by the AppServer for TLS (delta-bin/config/tls-cets/keystore.jks)
Which is then passed into the Tomcat process via the Java -javax.net.ssl.trustStore property.
Tomcat SSL Configuration - Windows
Tomcat Configuration
Tomcat by default is configured with a http connector. An SSL connector is required
To add the SSL connector open %CATALINA_HOME%confserver.xml and create a new definition below the current http one
Ensure that both the keystoreFile and keystorePass have been updated in the server.xml to the full path to the keystore and password you entered when running the command in step 1. The server.xml file will look similar to below but must be your own path and password:
Modify http connector to redirect to SSL
Modify web.xml to only all HTTPS connections, open %CATALINA_HOME%confweb.xml and append the to the 'Default Session Configuration' within the web.xml:
Tomcat URLs
When deployed with SSL, Tomcat will use the TOMCAT_SECURE_PORT value as the port for the HTTPS/SSL connector. The HTTP port (TOMCAT_PORT) will redirect to the HTTPS/SSL port.
Tomcat HTTPS with kdb+ TLS
If you are deploying with TLS enabled for kdb+ and HTTPS enabled for Tomcat there are additional considerations. For both of these to work the install script needs to export the cert used for the HTTPS connector out of the keystore defined below:
If you have created the keystore using the instructions above the certificate extracted will have the alias 'tomcat'. Drupal 8 docker download. The install log will contain:
If you are using a keystore which contains a different alias for the key, the install will fail and you will see the following:
With the alias changed you should see:
The connector cert is then imported into the keystore used by the AppServer for TLS (delta-bin/config/tls-cets/keystore.jks)
Which is then passed into the Tomcat process via the Java -javax.net.ssl.trustStore property.
Tomcat SSL Configuration - Windows
Tomcat Configuration
Tomcat by default is configured with a http connector. An SSL connector is required
To add the SSL connector open %CATALINA_HOME%confserver.xml and create a new definition below the current http one
Ensure that both the keystoreFile and keystorePass have been updated in the server.xml to the full path to the keystore and password you entered when running the command in step 1. The server.xml file will look similar to below but must be your own path and password:
Modify http connector to redirect to SSL
Modify web.xml to only all HTTPS connections, open %CATALINA_HOME%confweb.xml and append the to the 'Default Session Configuration' within the web.xml:
Tomcat URLs
When deployed with SSL, Tomcat will use the TOMCAT_SECURE_PORT value as the port for the HTTPS/SSL connector. The HTTP port (TOMCAT_PORT) will redirect to the HTTPS/SSL port.
HTTP URL
e.g.
HTTPS URL
e.g.
AppServer filters - Content-Security-Policy
By default the feature is turned off and requires the following manual steps to activate:
Create A New Keystore
- Update env variable
APPSERVER_CONTENT_SECURITY_POLICYindelta.profile. Default value is OFF. To enable Content-Security-Policy header, set to ON. To enable Content-Security-Policy-Report-Only header, set to REPORTONLY. - Edit
web.xml(in$TOMCAT_HOME/latest/confdirectory) to include xml defining the Content Security Policy Header Filter. (Example xml is given below). - In
$TOMCAT_HOME/latest/libdirectory, run
- Copy the file
webapps/ROOT/WEB-INF/classes/com/fd/server/filters/ContentSecurityPolicyHeaderFilter.classto the filters directory created in previous step. - Restart Appserver.
Example XML (note this is an example and end-user needs to determine the correct settings to use for their own deployment).

